
Broad Context Detection™
The broader context of targeted attacks becomes instantly visible on a timeline with all impacted hosts, relevant events and recommended actions.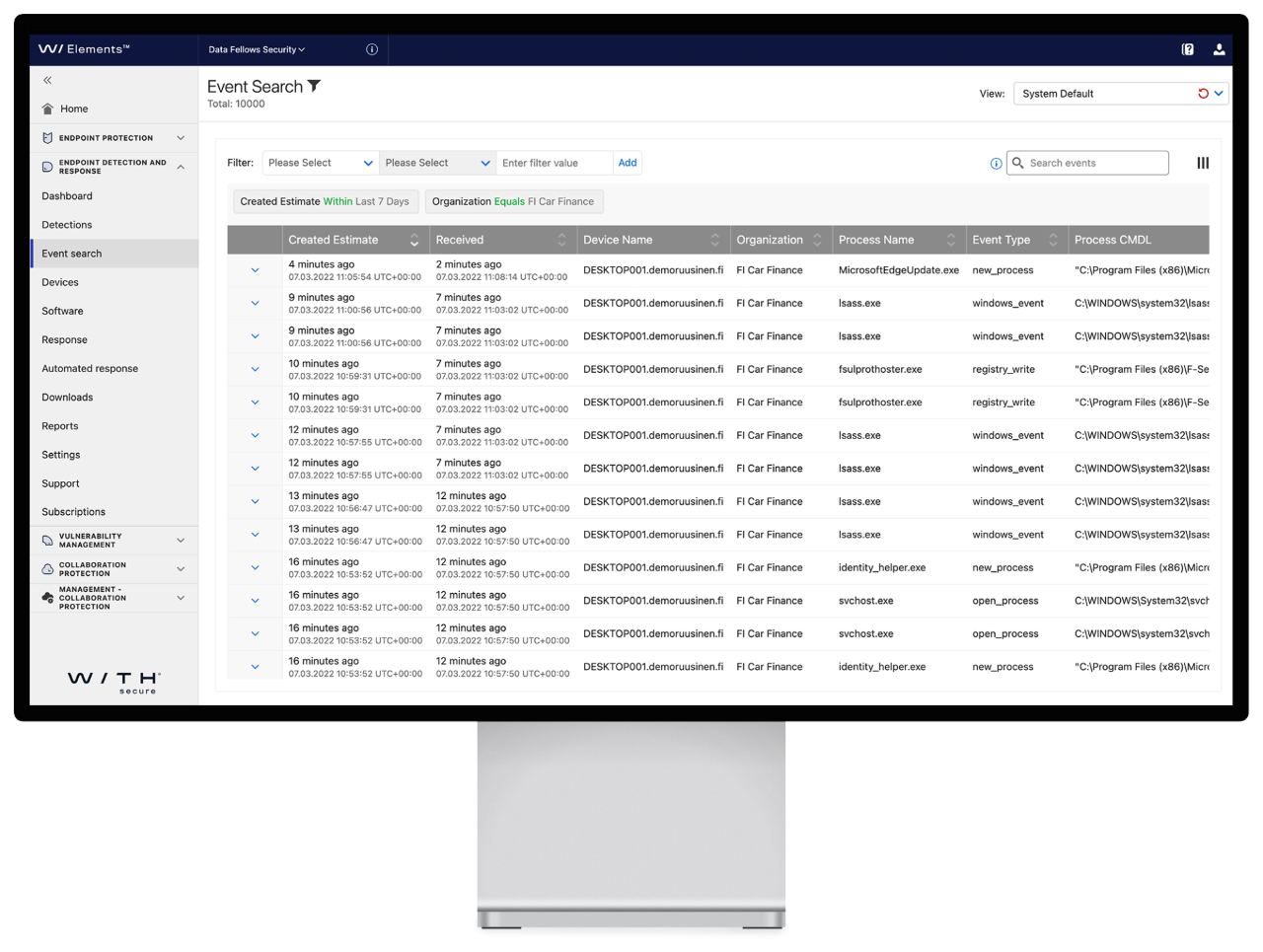
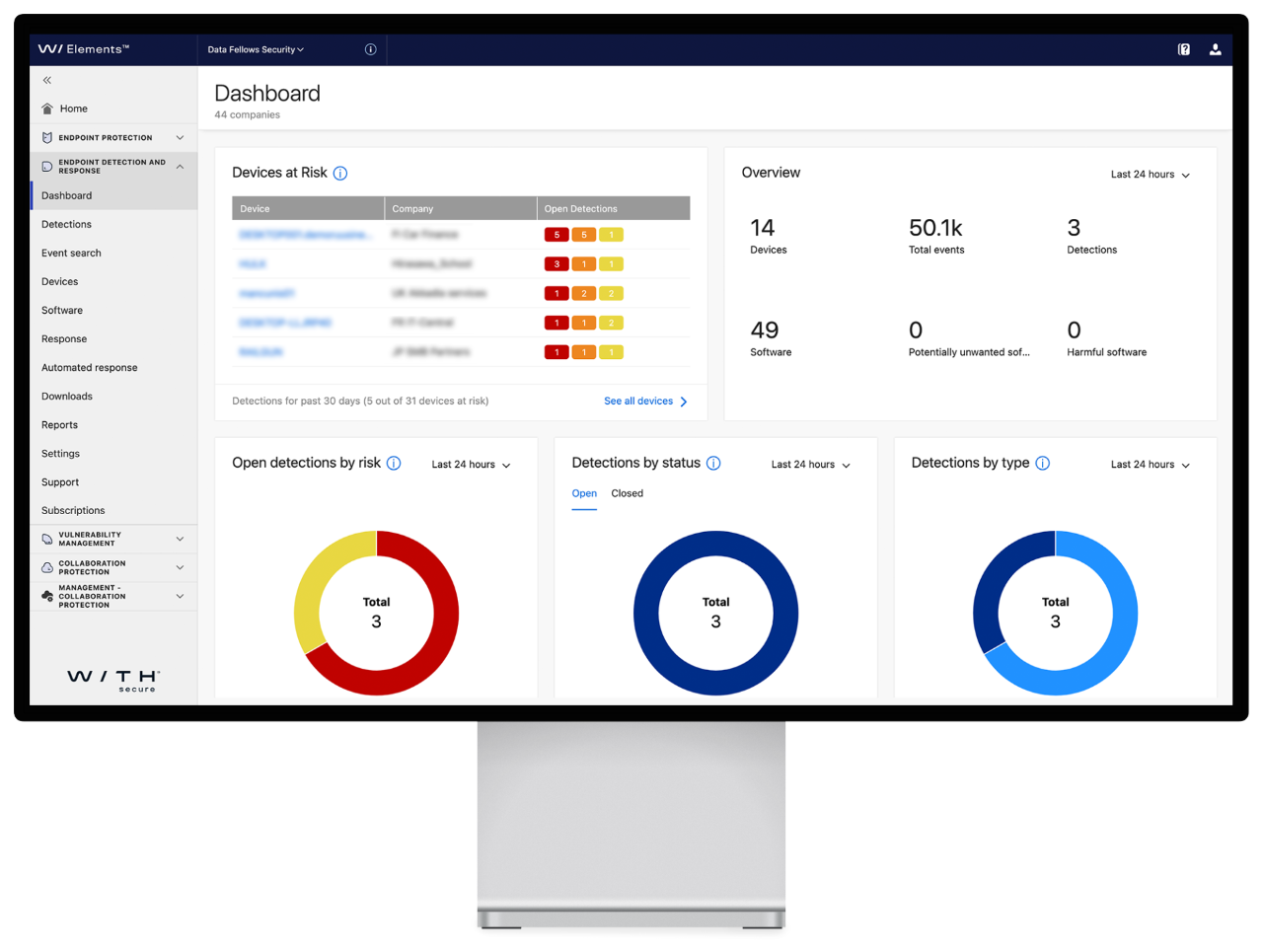
Event Search
With this built-in feature you can view, search, and explore the event data collected from your company endpoints that are related to any Broad Context Detections.Elevate to WithSecure
Some detections require deeper threat analysis and guidance by specialized cyber security experts. For these tough cases, the solution has a unique built-in "Elevate to WithSecure" service. It offers professional incident analysis of methods and technologies, network routes, traffic origins, and timelines of Broad Context Detection™ to provide expert advice and further response guidance whenever under attack.Automated Response
Automated response actions can be used to reduce the impact of targeted cyber attacks by containing them around the clock whenever risk levels are high enough. This automation is designed specifically to support teams only available during business hours, also taking the criticality of detections into account.Host Isolation
Stopping breaches as early as possible is paramount, and with Host isolation, this can be achieved. When a breach is detected the host affected can be automatically or manually isolated from the network, stopping the attacker from using the host.